61.2% of Canadian organizations were confronted by a ransomware attack
With the average cost of $6.35 million to Canadian companies of a data breach and the average ransomware payment of $200,000, protecting your organization from cyber-attacks must now be seen as a priority.
Ransomware is often installed when an employee clicks on a link in phishing email or visits an effected website and then unknowingly downloads and installs malware. In 2021, Canada ranked 11th in the number of ransomware threats and financial gain remains the primary motivation for these attacks.
Phishing emails come in many forms, including:
- Account Takeovers – when a bad actor takes over your account by discovering your online credentials – often for financial gain or credit card fraud
- Brand Impersonation – impersonating your brand as a ploy to gain personal and sensitive information
- Spear Phishing – an email from what appears to be a trusted source that contains a link or download that gives the attacker access to confidential information
- Business Email Compromise (BEC) – is a spear-phishing attack that targets employees with the goal of having them transfer money from the business to the attacker.
- CEO Fraud – another spear-phishing attack; the hacker attempts to impersonate the CEO in an effort to gain sensitive data or a funds transfer
- Malware – a catchall term for malicious software – designed to attack, hurt or destroy your network. Malware includes trojans, virus, worms, and more.
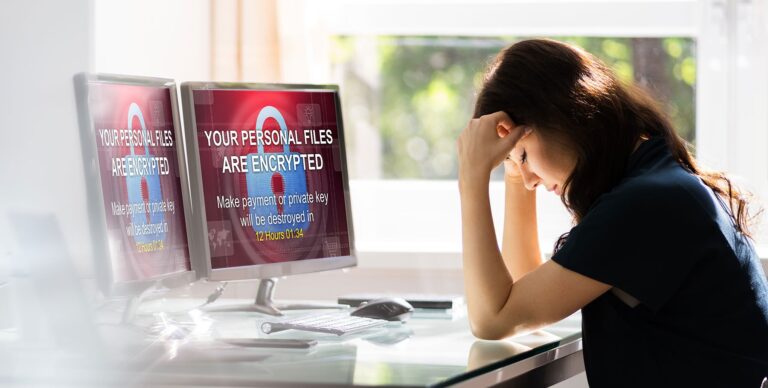
- Ransomware – a type of malware that often either locks your organizations information or threatens to make it public unless a ransom is paid.
- Zero-Day Attacks – when a hacker exploits an unknown software vulnerability.
To help defend yourselves and others in the fight against email phishing, the U.S. Cybersecurity and Infrastructure Security Agency (CISA)’s Phishing Tips Sheet urges to do the following:
Play hard to get with strangers. Links in email and online posts are often the way cybercriminals compromise your computer. If you’re unsure who an email is from—even if the details appear accurate—do not respond, and do not click on any links or attachments found in that email. Be cautious of generic greetings such as “Hello Bank Customer,” as these are often signs of phishing attempts. If you are concerned about the legitimacy of an email, call the company directly.
Think before you act. Be wary of communications that implore you to act immediately. Many phishing emails attempt to create a sense of urgency, causing the recipient to fear their account or information is in jeopardy. If you receive a suspicious email that appears to be from someone you know, reach out to that person directly on a separate secure platform. If the email comes from an organization but still looks “phishy,” reach out to them via customer service to verify the communication.
Protect your personal information. If people contacting you have key details from your life—your job title, multiple email addresses, full name, and more that you may have published online somewhere—they can attempt a direct spear-phishing attack on you. Cybercriminals can also use social engineering with these details to try to manipulate you into skipping normal security protocols.
Be wary of hyperlinks. Avoid clicking on hyperlinks in emails and hover over links to verify authenticity. Also, ensure that URLs begin with “https.” The “s” indicates encryption is enabled to protect users’ information.
Double your login protection. Enable multi-factor authentication (MFA) to ensure that the only person who has access to your account is you. Use it for email, banking, social media, and any other service that requires logging in. If MFA is an option, enable it by using a trusted mobile device, such as your smartphone, an authenticator app, or a secure token—a small physical device that can hook onto your key ring.
Shake up your password protocol. According to the National Institute of Standards and Technology guidance, you should consider using the longest password or passphrase permissible. Get creative and customize your standard password for different sites, which can prevent cybercriminals from gaining access to these accounts and protect you in the event of a breach. Use password managers to generate and remember different, complex passwords for each of your accounts.
Install and update anti-virus software. Make sure all of your computers, Internet of Things devices, phones, and tablets are equipped with regularly updated antivirus software, firewalls, email filters, and anti-spyware.
The Canadian Centre for Cyber Security also advises organizations to adopt a defense in depth (multi-layer) strategy to protect their devices, systems, and networks from ransomware, malware and cyber attacks:
- Implement a comprehensive backup plan for your organization, including an offline backup process
- Develop an incident response plan and a disaster recovery plan
- Manage user and administrator accounts
- Layer security controls throughout your network
- Establish perimeter defences
- Implement logging and alerting
- Conduct penetration testing
- Segment your networks
- Constrain scripting environments and disable macros
- Patch and update
- Create an application allow list
- Use a protective domain name system (DNS)
- Apply password management
- Use email domain protection
Obviously, this is a lot for small- and medium-sized businesses to implement on their own.
Interface Technologies’ Cybersecurity is the industry’s best solution for your organization’s security. Cost-effective and powerful, Interface protection can be implemented quickly, regardless of whether your employees work at the office or remotely.
We know how to prevent Ransomware, and if that fails, we are experts in maintaining a brick house of security on the backups. When a client has no backup, we know how to take it from there. We have never made an insurance claim against our $5,000,000 Cybersecurity coverage.
From Vulnerability Assesment and Penetration Testing to Disaster Recovery Plans to Cyber Training and Compliance – Interface Technologies will empower your organization’s cyber defences.
Request and schedule a free Interface Cybersecurity demonstration. It’s the best way to protect your company and the best cyber decision you can make in the phight against phishing.